AI-Powered Cybersecurity: How Frontier Models Are Transforming Defense
As artificial intelligence reaches new frontiers, the cybersecurity landscape is undergoing a profound transformation. Recent advancements from labs like OpenAI and Anthropic are not just incremental improvements—they signal a paradigm shift toward AI-native defense systems. SentinelOne, a pioneer in autonomous security, has been collaborating with these labs for years, embedding cutting-edge AI into its platform. In this Q&A, we explore how frontier AI models are accelerating automated threat response, bridging the gap between vulnerability discovery and real-world risk, and why machine-speed defense is the future. Learn about the reshaping of cyber defense, the role of partnerships, and more.
How are frontier AI models reshaping cybersecurity defense?
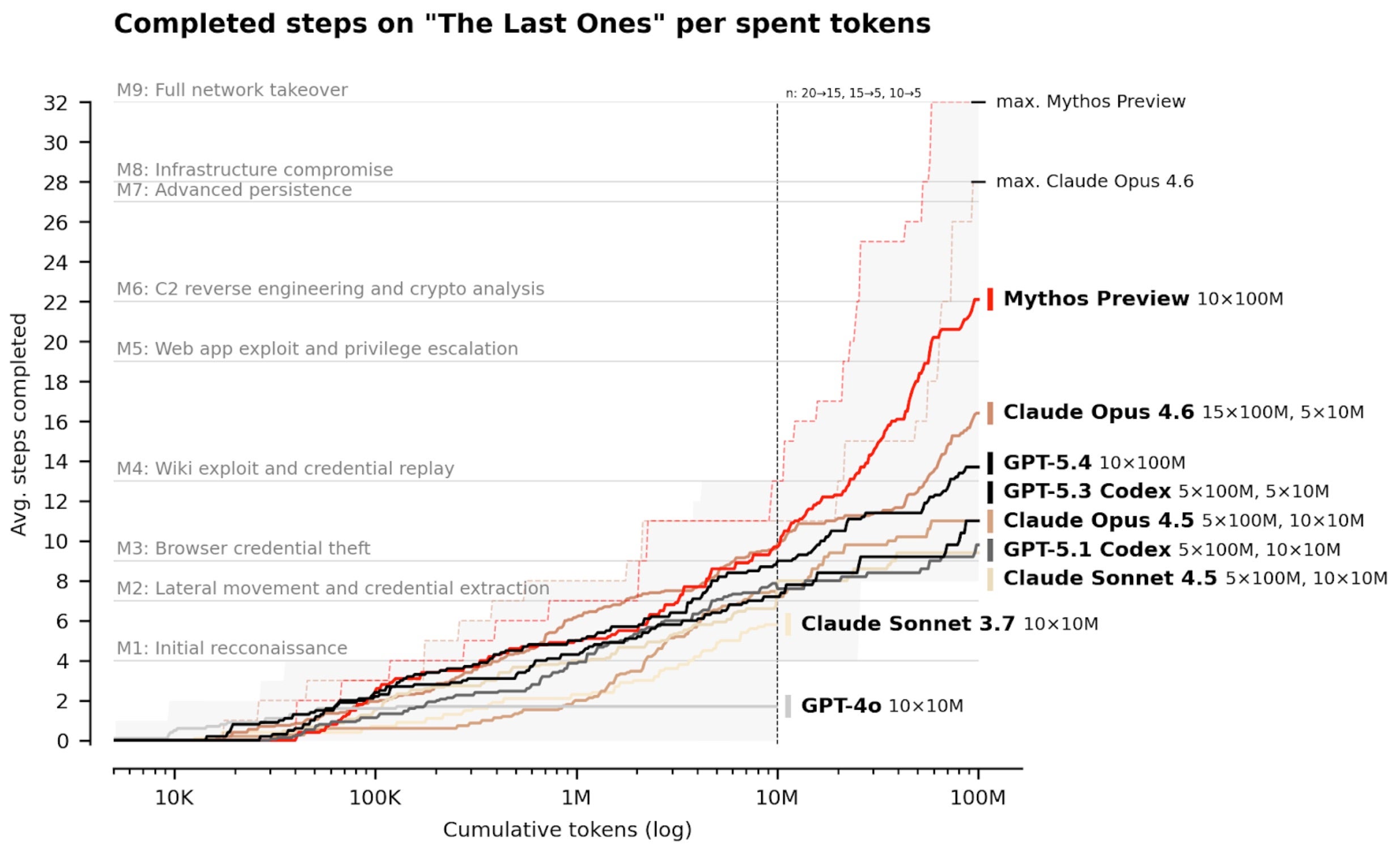
Frontier AI models, such as those from OpenAI, Anthropic, and Google DeepMind, are fundamentally reshaping cybersecurity by enabling faster, smarter, and more automated security operations. These advanced models improve how defenders identify weaknesses, analyze complex systems, and reason about attack paths at scale. At the same time, they empower attackers to discover vulnerabilities with unprecedented speed. This dual-edge dynamic intensifies the race, but it also drives innovation in defense. For instance, SentinelOne integrates insights from these labs into its platform, using behavioral AI and automation to detect and respond to threats at machine speed. This shift from manual, reactive approaches to proactive, autonomous defense is crucial in an era where zero-day exploits emerge rapidly. Frontier AI doesn't just make existing tools better; it redefines the very architecture of cyber defense, emphasizing real-time, context-aware responses that adapt to novel threats.
What role do partnerships with AI labs play in SentinelOne's approach?
SentinelOne has maintained long-standing collaborations with leading frontier labs like OpenAI, Anthropic, and Google DeepMind. These partnerships provide invaluable insight into how advanced models evolve and where they can create meaningful impact in security. While specific details often remain confidential, the learnings are continuously embedded into SentinelOne's platform. For example, insights from these labs help SentinelOne refine its behavioral AI algorithms, improve threat detection accuracy, and enhance autonomous response capabilities. This symbiotic relationship ensures that SentinelOne stays at the forefront of AI innovation, translating cutting-edge research into practical defenses that protect customers from advanced attacks, including zero-day exploits that no other solution can stop. The partnership model also allows SentinelOne to anticipate future threats and adapt its architecture accordingly, maintaining an AI-native posture that is both proactive and resilient.
Why is the gap between vulnerability discovery and real-world risk important?
Discovering more vulnerabilities does not automatically translate to higher security. The gap between theoretical exposure and operational risk is often substantial. Many vulnerabilities are not meaningfully exploitable in live environments due to existing architectural layers, controls, mitigations, and runtime protections. For instance, a software bug might be critical in isolation but becomes irrelevant when network segmentation, endpoint detection, or behavioral monitoring blocks its exploitation. Understanding this gap is key for effective defense. Instead of chasing raw vulnerability counts, security teams must prioritize based on real-world conditions: which vulnerabilities are actually reachable, which assets are most valuable, and which attack paths are viable. SentinelOne's AI-native platform excels here by continuously analyzing live environments, correlating threat intelligence, and autonomously prioritizing and stopping actual attacks. This focus on operational risk rather than theoretical exposure is what makes AI-driven defense truly effective against novel threats and zero days.
How does SentinelOne's AI-native platform operate at machine speed?
From its inception, SentinelOne was built to operate at machine speed, leveraging behavioral AI, automation, and autonomous protection across multiple attack surfaces—endpoint, cloud, identity, data, network, and AI. Unlike traditional security tools that rely on signature-based detection or manual analysis, SentinelOne's platform continuously monitors system behavior, identifies anomalies in real-time, and initiates autonomous responses without human intervention. This machine-speed operation is critical for countering modern threats that evolve in seconds. For example, when a supply chain attack exploits a zero-day vulnerability, the platform can instantly detect the malicious behavior, isolate the affected system, and roll back changes—all in milliseconds. As frontier AI advances, the value of this approach grows because the same AI that powers attackers can be harnessed for faster, more intelligent defense. The result is a dynamic, self-adaptive security posture that stays ahead of adversaries.
Can you give examples of recent supply chain attacks stopped by autonomous response?
Yes, in recent weeks, SentinelOne's autonomous response has proven effective against supply chain attacks targeting LiteLLM, Axios, and CPU-Z. These attacks leveraged unpatched or zero-day vulnerabilities, exploiting trusted agents and workflows in the AI era. In each case, traditional signature-based defenses would have failed because the threats were novel and unknown. However, SentinelOne's behavioral AI detected the anomalous activities—such as unexpected process behaviors, file modifications, or network connections—and triggered an autonomous response at machine speed. The platform isolated compromised endpoints, blocked malicious payloads, and rolled back unauthorized changes without requiring human intervention. This capability to stop novel threats in real-time underscores why AI-native defense is essential. Supply chain attacks are particularly dangerous because they exploit trust relationships; autonomous, behavioral-based detection is often the only antidote when patching is not immediately possible.
How do frontier AI models benefit both defenders and attackers?
Frontier AI models are a double-edged sword in cybersecurity. On the one hand, they empower defenders by improving vulnerability identification, system analysis, and attack path reasoning at scale. These models can process vast amounts of data, detect subtle patterns, and recommend mitigations faster than humans. On the other hand, attackers gain similar advantages: they can use AI to discover zero-day vulnerabilities more rapidly, craft sophisticated phishing campaigns, and automate attack chains. This symmetry accelerates the arms race. However, SentinelOne argues that raw vulnerability counts do not equate to real risk because many theoretical exposures are not practically exploitable. The key is to focus on operational defense—using AI to understand real conditions, prioritize what matters, and stop actual attacks. By embedding frontier AI insights into an autonomous platform, SentinelOne tilts the balance back in favor of defenders, ensuring that machine speed works for protection, not just exploitation.
What makes AI-native defense superior to traditional cybersecurity approaches?
Traditional cybersecurity approaches often rely on signature-based detection, manual analysis, and periodic updates, which are too slow to counter modern, fast-evolving threats. In contrast, AI-native defense is inherently adaptive and operates at machine speed. It uses behavioral AI to understand normal patterns and instantly flag anomalies, enabling autonomous response to novel attacks—including zero-days—without waiting for patches or human oversight. AI-native platforms like SentinelOne also integrate across all attack surfaces (endpoint, cloud, identity, data, network, AI) providing holistic visibility and coordinated response. The real advantage lies in closing the gap between vulnerability discovery and operational risk: instead of chasing every CVE, AI-native defense focuses on what matters in live environments. As frontier AI advances, this approach becomes even more powerful, leveraging the same breakthroughs that help attackers to fortify defenses. The shift from reactive to proactive, autonomous security is the future, and AI-native platforms are leading the way.